Assaults on the software program provide chain are underway, shaking the cryptocurrency ecosystem by means of JavaScript. In line with a bunch of laptop vulnerability researchers writing below the title JDSTAERK, numerous NPM improvement packages (node packages) have been topic to malicious updates.
Researchers would have found that the developer's account often called “qix” was violated and allowed. Malicious code distribution for instruments that accumulate over 47 million downloads Each week. Though it’s primarily a JavaScript developer throughout the Web, assaults can not directly have an effect on finish customers and compromise cryptocurrency wallets.
The incident comes from the NPM repository, a platform that homes open supply packages which are important for creating JavaScript functions.
These packages are utilized in 1000’s of tasks all over the world and are frequent dependencies for servers and net functions. The dedicated account would have allowed the attacker Publish modified variations of in style packagesintroduces malicious code designed to steal stealth when stealing cryptocurrency funds.
In line with an evaluation posted on the jdstaerk.substack.com weblog, malware is particularly activated when it detects the presence of cryptocurrency wallets as meta masks.
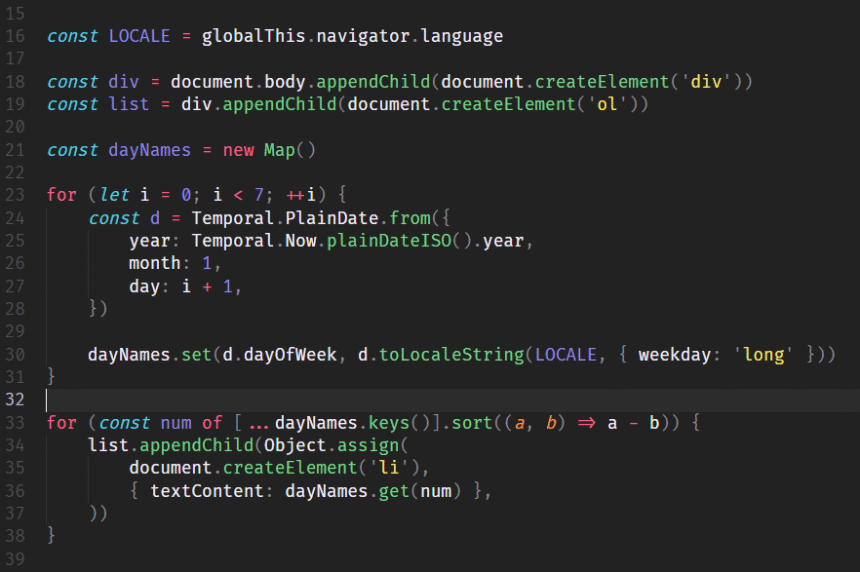
Malicious code works in two phases. If the pockets can’t be discovered, it makes an attempt to run a passive assault to ship information to an exterior server. Nevertheless, detecting an energetic pockets presents an actual danger. On this situation, malware intercepts communication between the pockets and the person. Function precise time transactions from the working system clipboard.
Researchers clarify the fraudulent course of in additional element.
When a person begins a transaction (for instance, ETH_SENDTRANSACTION), malware intercepts the information earlier than sending it to the pockets for signature. It then adjustments the transaction in reminiscence and replaces the reputable receiver orientation with the attacker orientation. The manipulated transaction is transferred to the person's pockets for approval. If the person doesn’t meticulously affirm the affirmation display handle, they signal a transaction that sends funds on to the attacker.
Jdstaerk, group of investigators.
Though the end-user is just not a direct goal, the ever-present presence of those packages in software program tasks amplifies danger. This isn’t talked about instantly within the JDSTAERK evaluation.
Charles Guillemett, CTO de Ledger, and who mirrored the information, it warns it Solely customers who use pockets {hardware} and might carry out seen, safe signature processes are protected Earlier than the software program provide chain assault.
(tagstotranslate) Cyber Assault