Acurast, a smartphone-based distributed confidential computing challenge, has raised $11 million by claiming tamper-resistant execution and safe {hardware} verification on client cellphones.
Based on an announcement Thursday shared with Cointelegraph, Acurast has raised $11 million from Ethereum co-founder and Polkadot founder Gavin Wooden, MN Capital founder Michael van de Poppe, GlueNet founder Ogle and others. The challenge goals to launch its mainnet on November seventeenth, and also will launch its native token ACU on the identical time.
Acurast founder Alessandro De Carli mentioned that “billions of smartphones are essentially the most battle-tested {hardware} on the planet” and that the corporate desires to cut back prices by leveraging them for “verifiable delicate computing.”
Community Explorer stories that almost 150,000 telephones have already joined the community, processing greater than 494 million transactions and enabling the deployment of almost 94,200 companies.
“We eradicate gatekeepers, cut back prices, and ship safe, trustless computing to anybody, anyplace, with out knowledge facilities,” De Carli asserted.

Acurast community knowledge. sauce: acurast
Associated: Decentralized computing networks democratize world AI entry
Do you run delicate computing on third-party {hardware}?
Acurast says this can enable anybody to supply confidential computing (a person with bodily entry to a smartphone operating the Node software program is not going to have entry to the information used within the calculations). This requires a setup that ensures with a excessive diploma of certainty that the smartphone proprietor can not modify the software program in a manner that compromises this confidentiality.
To realize this goal, the challenge's builders carried out a sequence of checks to make sure that the smartphone runs manufacturer-approved software program that doesn’t compromise safety conditions. Nonetheless, related countermeasures have been applied by banking app builders for years, just for customized firmware communities comparable to Graphene OS to search out workarounds that enable functions to run on unauthorized setups. De Carli mentioned this isn’t the case with Acurast's app.
De Carli informed Cointelegraph that the Acurast processor utility sends a hardware-backed key pair together with key attestation to the Acurast protocol. If these don’t match these supplied by your smartphone producer, then the message “The Acurst processor can not get hold of legitimate authorization and can’t take part within the community.”
“This ensures that solely real and authorized {hardware} might be onboarded,” De Carli mentioned, including that unsuitable environments “can’t be onboarded as a result of the signed certificates hooked up to the hot button is not retrieved,” that means the cellphone proprietor can not tamper with person knowledge or the execution setting.
Associated: Dubai strikes in the direction of machine financial system regulation with DePIN Peak community
Safety restrictions
Nonetheless, if a manufacturer-approved smartphone working system (iOS or Android) is exploited in the precise manner by malware or its rightful proprietor, the safety assumption is damaged.
De Carli largely dismissed this concept, saying, “If you could find an exploit that permits you to do this, you're successfully eligible for a multi-million greenback bounty, and that exploit will then be fastened rapidly,” citing Google's bug bounty program for instance.
Nonetheless, such vulnerabilities have certainly been found up to now.
For instance, in Samsung's TrustZone working system, a keymaster AES-GCM IV reuse assault was found in 2022, permitting the extraction of protected keys and exploitation of authentication. Moreover, an attacker who has already compromised the app's course of or kernel might be able to encrypt and decrypt the content material, however not the non-public key itself.
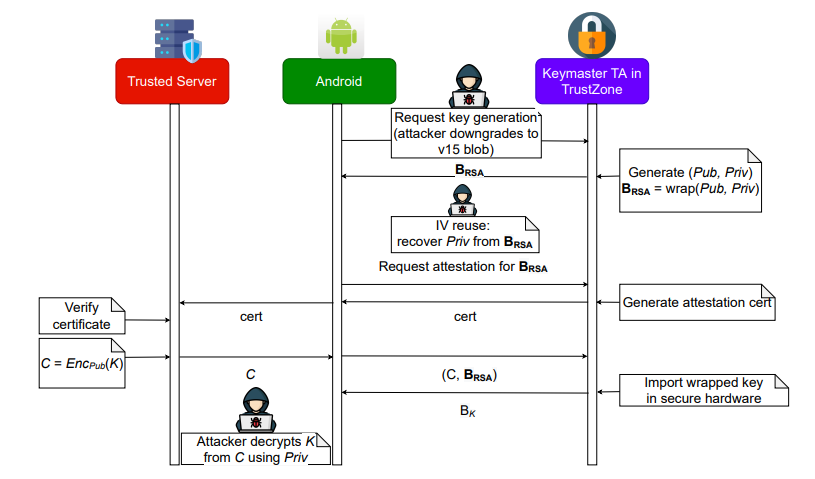
AES-GCM IV reuse assault. sauce: USENIX
journal: The Subsequent Large Development in Blockchain: What to Watch


